How to Secure Healthcare Apps: Data Encryption, Access Control, and Compliance

Key Takeaways
- Zero Trust is Mandatory: Don’t just trust a login; use MFA everywhere and verify every user, every time, regardless of their location.
- Encrypt Everything: Go beyond the database. Protect data while it’s moving (APIs), sitting (backups/CSV exports), and processing (memory).
- Vendors are a Major Risk: Third-party breaches are spiking. A contract (BAA) isn’t enough; you need to audit their security before and during the partnership.
- Security by Design: Stop “bolting on” security at the end. Use threat modeling and automated testing while the code is actually being written.
- The 90-Day Fix: Start with a risk assessment (Month 1), hit the quick wins like MFA (Month 2), and then move to advanced network shielding (Month 3).
It’s 2 AM, and you get that one dreaded call. Your security team just detected unusual activity in your patient portal. By morning, you’re looking at a potential HIPAA violation that could affect thousands of patients. The board wants answers. Your legal team is already drafting notifications. And you’re wondering how a single security gap just became a multi-million-dollar problem.
If this scenario feels uncomfortably familiar, you’re not alone. In 2025, healthcare experienced 710 large data breaches affecting nearly 62 million individuals, and that cost an average of $7.42 million per incident, making them the costliest of any industry. For healthcare CTOs, the question is how to build defenses that actually hold up under real-world attacks.
The reality is that healthcare mobile app protection isn’t just about checking compliance boxes anymore. It’s about architecting systems that can withstand increasingly sophisticated threats while still delivering the seamless user experience your clinicians and patients expect. Let’s talk about how to actually do that.
Why Healthcare Apps Are Prime Targets (And Why Traditional Security Isn’t Enough)
Healthcare apps are basically treasure troves for cybercriminals. A single patient record on the dark web can fetch up to 50 times more than a credit card number. Why? Because health records contain everything: Social Security numbers, insurance details, medical history, and billing information. It’s one-stop shopping for identity theft.
But here’s what keeps me up at night as someone who’s worked with countless healthcare app development companies in the USA and UK: most organizations are still relying on security frameworks designed for a different era. Like: perimeter security, basic encryption, maybe some two-factor authentication if you’re feeling fancy. The problem? Modern attacks don’t work that way anymore.
Consider these sobering facts from 2025:
- The average initial ransom demand for healthcare targets hit $18.2 million, six times higher than the education or energy sectors
- Third-party vendor breaches increased 42% year-over-year, with many organizations having no visibility into their business associates’ security posture
- The average time to detect a breach was 78 days, which is over two months, during which attackers had free rein in your systems
The attack surface has exploded. We’re not just securing a single EMR system anymore. We’re protecting patient portals, telehealth platforms, mobile apps for everything from medication adherence to remote monitoring, API connections to labs and pharmacies, and integration points with business associates you might not even know about. Each one is a potential entry point.
This is exactly why working with experienced healthcare mobile app development services like Tech Exactly, that understand the nuanced security requirements, becomes critical. If you’re interested in seeing how these challenges manifest in real projects, take a look at our detailed case study on building an IEC 62304-compliant mobile app. It walks through the security architecture decisions we made when the stakes were highest.
Building a Modern Encryption Strategy That Actually Works
Alright, let’s talk encryption. And no, I don’t mean just checking a box that says “data encrypted at rest.” I mean building a comprehensive encryption strategy that covers every state of your data’s lifecycle because attackers don’t care about your compliance documentation; they care about finding that one unencrypted backup tape or API endpoint.
The Three States of Data (And How to Protect Each One)
Data at Rest: More Than Just Database Encryption
When data’s sitting in your databases, file systems, or backups, it needs to be encrypted with AES-256 or stronger. But most organizations encrypt the production database and call it a day. What about your backups? Development environments? Those CSV exports your analytics team runs? The temporary files your batch processes create?
I’ve seen organizations pass their HIPAA audits with flying colors, only to discover later that their backup vendor was storing unencrypted snapshots on S3. The compliance checkbox was marked, but the actual protection wasn’t there. This is where robust healthcare compliance app development practices come into play: you need encryption policies that follow your data everywhere it goes, not just where it lives in production.
Data in Transit: The API Security Gap
TLS 1.3 is your baseline here, and anything less is asking for trouble. But implementing TLS correctly is trickier than it sounds. You need to configure certificate pinning for your mobile apps, implement mutual TLS for server-to-server communications, and ensure that every API endpoint enforces encryption.
The tricky part? Many healthcare organizations have legacy systems that can’t handle modern TLS configurations. You end up with a choice: maintain backwards compatibility and accept the risk, or invest in upgrading those systems. There’s no good answer, but ignoring the problem isn’t an option. For a deeper dive into architecting these kinds of trade-offs, our article on security architecture for healthcare apps covers the decision-making framework we use.
Data in Use: The Forgotten Third State
This is where things get interesting. Data in use, meaning data being actively processed in memory or displayed on screens, has traditionally been the hardest to protect. Recent advances in confidential computing and homomorphic encryption are changing that, but they’re not quite ready for prime time in most healthcare applications.
What you can do right now: implement memory encryption in your mobile apps, use secure enclaves for processing sensitive operations, and ensure that sensitive data is cleared from memory immediately after use. It’s not perfect, but it’s significantly better than leaving PHI sitting in application memory indefinitely.
Healthcare Access Control: Beyond Username and Password
Let’s talk about healthcare access control: if encryption is your first line of defense, access control is your second, third, and fourth lines of defense. You can have the most sophisticated encryption in the world, but if someone can just log in with admin credentials they found on a sticky note, you’ve got problems.
Implementing Zero Trust Architecture
Zero trust is one of those terms that gets thrown around in every vendor pitch, but what does it actually mean for a healthcare CTO trying to secure patient data? At its core, it’s simple: never trust, always verify.
Here’s what zero trust looks like in practice:
- Multi-factor authentication (MFA) everywhere, and I mean everywhere. Not just for administrators, but for every user accessing any system with PHI. Yes, even doctors in the middle of rounds will complain. Yes, it’s still worth it.
- Contextual access policies that consider device health, location, time of access, and user behavior patterns. A physician accessing records at 3 AM from a coffee shop in a different state? That should trigger additional verification.
- Microsegmentation of your network. Your billing system shouldn’t be able to talk to your patient portal unless there’s a legitimate business need. Lateral movement is how small breaches become catastrophic ones.
- Continuous authentication that doesn’t just verify identity at login but throughout the entire session. Behavioral biometrics, session timeout policies, and real-time risk scoring all play a role here.
The challenge? Balancing security with usability. Push too hard on security controls, and you’ll have physicians writing passwords on their scrubs. Not hard enough, and you’re the next headline. This is where partnering with a Healthcare App Development Company in USA or a Healthcare App Development Company in UK that understands healthcare workflows becomes invaluable.
Role-Based Access Control (RBAC) That Reflects Reality
In theory, RBAC is straightforward: nurses see patient vitals, physicians see full records, billing staff see insurance information, and so on. In practice, healthcare is messy.
The mistake I see repeatedly is organizations implementing dozens of granular roles that become impossible to manage. You end up with role creep, where people accumulate permissions over time, and nobody has the authority or knowledge to clean them up. The better approach? Start with broad role categories based on job functions, then layer attribute-based access control (ABAC) on top for exceptions. You get the simplicity of RBAC with the flexibility of ABAC when you need it.
And don’t forget about emergency access protocols: what happens when a patient crashes and the covering physician needs immediate access to records they wouldn’t normally see? You need break-glass procedures that grant emergency access while logging every action for audit purposes.
Compliance: HIPAA, GDPR, and Everything in Between
Compliance isn’t security, but security without compliance is a recipe for regulatory nightmares. And if you’re operating internationally or even just considering expansion, you’re not just dealing with HIPAA anymore. You’ve got GDPR in Europe, PDPA in Singapore, PIPEDA in Canada, and a growing patchwork of state privacy laws in the US.
The good news? Many of these regulations overlap in their core requirements. They all want encryption, access controls, audit logging, breach notification procedures, and data minimization. The bad news? The devil is in the details, and those details can be dramatically different. For a comprehensive breakdown of what compliance actually looks like across jurisdictions, our guide on healthcare app compliance in the USA and UK walks through the specific requirements and how they interact.
What is The HIPAA Security Rule
Here’s what keeps OCR (the Office for Civil Rights) busy these days: risk analyses. In 2025, 76% of all HIPAA enforcement actions included penalties for risk analysis failures. Three-quarters of the time when OCR comes knocking, it’s because organizations either didn’t do a risk analysis or did one so poorly that it might as well not exist.
The other enforcement hot button is the Breach Notification Rule. You’ve got 60 days from discovery to notify OCR, affected individuals, and potentially the media. Miss that deadline and you’re looking at:
- Fines ranging from $100 to $50,000 per violation
- Criminal penalties for willful neglect
- State attorney general enforcement actions (which have increased 40% since 2023)
- Reputational damage that’s hard to quantify but very real
The average HIPAA settlement in 2025 was $1.2 million, and that’s just the direct penalty. Factor in notification costs, credit monitoring, legal fees, and lost business, and you’re easily in the $7-10 million range.
Business Associate Agreements: Your Compliance Weak Link
Here’s a sobering fact: vendor and third-party breaches jumped 30% in 2025. Your cloud hosting provider, your medical transcription service, your patient engagement platform, they all have access to PHI, which means they’re all potential breach vectors.
A Business Associate Agreement (BAA) is not a security control. It’s a contract that says, “if you breach our patients’ data, we can sue you.” That’s important, but it doesn’t prevent the breach.
What you really need is:
- Security assessments before onboarding any vendor
- Annual security reviews of critical vendors
- Contractual requirements for security controls, not just compliance documentation
- Breach notification requirements that give you time to respond
- Data minimization: only share the minimum PHI necessary
If you’re building patient-facing applications, the vendor management piece becomes even more critical. Our case study on HIPAA-compliant website development shows how we approached vendor selection and BAA management for a therapy platform where security couldn’t be an afterthought.
Practical Implementation: Where to Start
Alright, so you’re convinced that security matters (hopefully you were already convinced), and you understand the major components. But where do you actually start? You can’t fix everything at once, and trying to will just lead to half-implemented controls that don’t protect anything.
The 90-Day Security Sprint
Month 1: Visibility and Assessment
You can’t protect what you can’t see. Start by mapping every system, application, and data flow that touches PHI. Yes, it’s tedious. Yes, you’ll discover things you didn’t know existed. That’s the point. Conduct a proper risk analysis, not a checkbox exercise, but a genuine assessment of vulnerabilities and threats. Inventory your business associates and review their security postures. This month is about understanding your current state.
Month 2: Quick Wins and Foundation
Implement MFA everywhere. Not just for administrators, but for every user. This single control will block the majority of credential-based attacks. Patch critical vulnerabilities, start with internet-facing systems and work inward. Enable logging and monitoring for all systems with PHI. You need visibility before you can have an effective incident response. Review and update your incident response plan, and actually test it with a tabletop exercise.
Month 3: Strategic Improvements
Start implementing zero trust principles for your highest-risk systems. Roll out endpoint detection and response (EDR) solutions. Conduct security training for all staff and make it engaging, not just compliance theater. Begin the process of segmenting your network based on data sensitivity. Review and remediate the findings from your month 1 risk analysis.
For organizations facing unique challenges, our article on healthcare software development challenges in 2026 provides additional context on common pitfalls and how to avoid them.
Building Security Into Development (Not Bolting It On Later)
If you’re developing new applications or substantially updating existing ones, security can’t be an afterthought.
What this looks like in practice:
- Threat modeling during the design phase, before writing a single line of code
- Security requirements built into user stories and acceptance criteria
- Automated security testing integrated into your CI/CD pipeline
- Code reviews that include security as a primary consideration
- Penetration testing before production deployment, not after
The challenge here is finding development partners who actually understand healthcare security, not just general web development. When evaluating potential partners for healthcare mobile app development services, ask them about their security practices. If they can’t articulate their threat modeling process or don’t have examples of HIPAA-compliant applications they’ve built, keep looking.
The Cost of Getting It Wrong
Let’s talk dollars and cents, because that’s ultimately what the board cares about. We’ve already mentioned that healthcare breaches average $7.42 million. But that’s just an average. The Change Healthcare breach in 2024 affected 193 million people and likely cost billions when you factor in system downtime, remediation, lawsuits, and regulatory penalties.
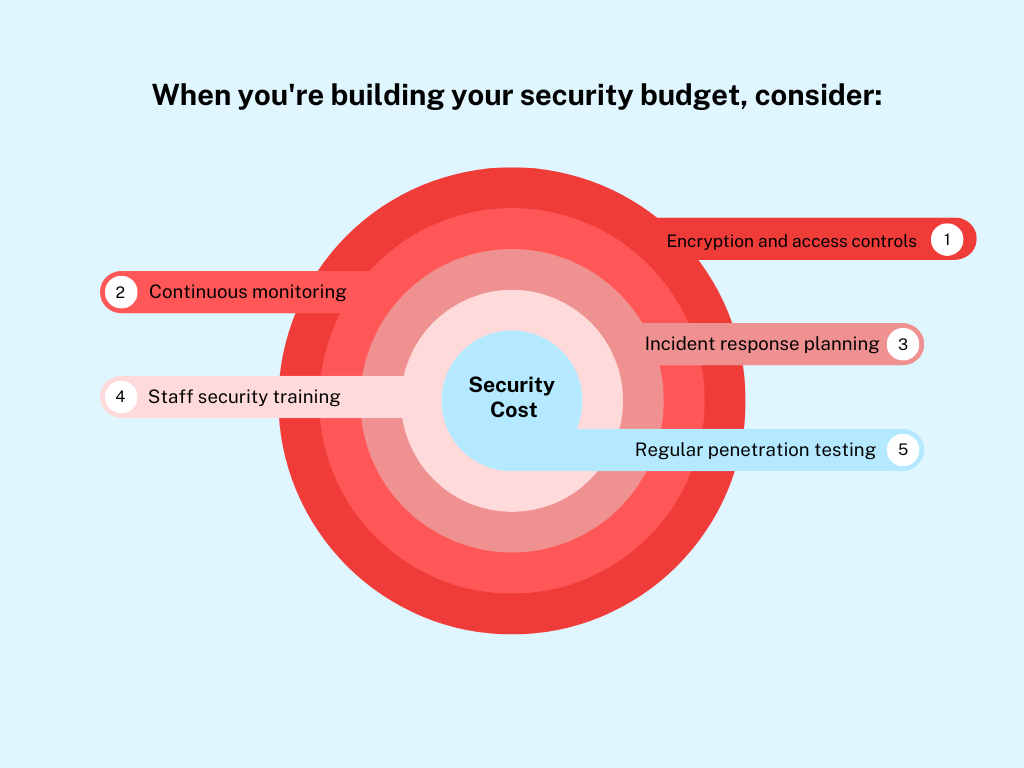
Security is expensive. But it’s nowhere near as expensive as a breach.
Yes, this adds up. A robust security program for a mid-sized healthcare organization might run $500K-$2M annually. But compare that to the $7.42 million average breach cost, and suddenly it looks like a bargain. And that’s before you factor in the reputational damage, loss of patient trust, and potential impact on clinical operations.
For organizations looking at major development or modernization projects, understanding the full compliance cost is critical. Our guide on patient portal development cost and compliance breaks down the security and compliance components so you can budget appropriately.
The Bottom Line:
Look, I get it. You’re juggling a million priorities. You’ve got legacy systems that need replacing, integration projects that are behind schedule, a board that wants to see ROI on every dollar spent, and clinicians who just want technology that works without jumping through security hoops.
But here’s the thing: security isn’t optional anymore. But you don’t have to solve everything at once. Start with the basics: encryption, access controls, and compliance. Build a solid foundation. Then iterate and improve. Work with partners like Tech Exactly, who understand healthcare security, whether that’s a Healthcare App Development Company in USA, a Healthcare App Development Company in UK, or specialized security consultants who live and breathe HIPAA.
Remember that 2 AM phone call I mentioned at the beginning? With the right healthcare mobile app protection strategies in place, that call becomes much less likely. And if it does come, you’re prepared to respond quickly, minimize the damage, and protect your patients’ data. That’s the difference between a security incident and a catastrophic breach.
Your move, CTO. The threats aren’t waiting, and neither should your security program. If you are interested in knowing more, please write to us at info@techexactly.com
Let's Start Your Project Today
Ready to build your App with us? Reach out now – our experts are just one click away.
Frequently Asked Questions
There is no single control that is enough on its own, but strong encryption combined with robust access control (especially MFA and role-based access) forms the foundation. Without these, even compliant systems remain vulnerable.
HIPAA enforces standards like encryption, audit logs, and risk assessments. While compliance does not guarantee security, it ensures a structured baseline that reduces the likelihood of breaches and regulatory penalties.
Healthcare apps store highly sensitive data, including medical records and personal identifiers, which are far more valuable on the dark web than financial data. This makes them a prime target for ransomware and identity theft.
Security audits should be conducted at least annually, with continuous monitoring in place. Additionally, audits are essential after major updates, integrations, or changes in compliance requirements.
Venkatesh Kannan is a Lead Business Analyst at Tech Exactly with 6+ years of experience in aligning technology with business strategy. He focuses on Generative AI adoption, modular architectures, and process-driven digital innovation.