Designing Multi-Tenant SaaS Applications: Trade-Offs, Pitfalls, and Best Practices

TL;DR
Short on time? Read this summary, then jump to the sections that matter to you.
- Multi-tenancy is an architectural decision. Every layer: API gateway, application logic, database queries, and background jobs must be tenant-aware from day one.
- Your isolation model sets your cost, compliance ceiling, and operational complexity. Shared schema is the cheapest but riskiest. Database-per-tenant is safest but most expensive. Most mature SaaS products land on a hybrid and build the tiering into their pricing.
- The noisy neighbor problem won’t show up in testing; it shows up in production. One tenant’s heavy query can time out every other customer on the same instance.
- The most expensive pitfalls are process gaps. Manual provisioning, single-tenant migration tooling, missing audit trails, and hardcoded tenant limits are what create the rework bills six months into growth.
- Design for offboarding before a customer asks for it. If your architecture can’t answer “where is this tenant’s data and how do we remove all of it” with a documented, automated process, that’s a live compliance liability.
Building a SaaS product that serves hundreds or thousands of customers on a single infrastructure is one of the most rewarding architectural decisions you can make (and one of the most unforgiving if you get it wrong).
We’ve seen both outcomes. Our developers at Tech Exactly have designed multi-tenant systems from scratch that scaled cleanly from 50 to 5,000 tenants without a major rearchitecture. We’ve also inherited codebases where saas multi tenant architecture was retrofitted after launch, and the rework cost the team months they didn’t have. The difference almost always came down to decisions made in the first two weeks: which isolation model to use, how to route tenants, and where to draw the boundary between shared and dedicated resources.
This blog is the guide we wish had existed when we started. It’s not a surface-level overview, but it has architecture thinking, the trade-off analysis, and the pitfalls that only become obvious after you’ve been burned by them.
The worldwide SaaS market is heading toward $315 billion in 2026, driven by AI monetization and usage-based pricing. And over 70% of modern SaaS vendors opt for some form of multi tenant architecture.
What Does Multi Tenancy Mean and How to Build a Multi-Tenant SaaS Application
What does multi tenancy mean? It means a single application instance serves multiple customers (tenants) while keeping their data and configurations isolated. Tenants share the same codebase and infrastructure, but experience it as their own secure environment.
Multi tenant meaning is often confused with “shared hosting,” but the distinction matters architecturally. Multi-tenancy is an intentional design pattern, not just a cost-saving deployment decision. It requires every layer of your stack: API gateway, application logic, data access layer, queue workers, caching, and analytics to be tenant-aware from the start.
Multi-tenant SaaS can lower the total cost of ownership by up to 40%. Efficient resource pooling reduces infrastructure waste by over 30% compared to single-tenant deployments. Those economics are the reason saas multi tenant is the default model for scalable B2B products.
Steps to Build a Multi-Tenant SaaS Application

Building a multi-tenant SaaS application involves designing a shared infrastructure where multiple tenants can operate securely and efficiently.
- Architect infrastructure
- Define tenant policies
- Choose a cloud platform
- Set up CI/CD
- Enable onboarding
- Apply authorization
- Configure routing
The Three Isolation Models: Understanding the Real Trade-Offs
Cloud multi tenancy isn’t a single pattern. There’s a spectrum of isolation approaches, and the right choice depends on your tenant profile, compliance requirements, and team’s operational maturity. Here’s how we think about it.
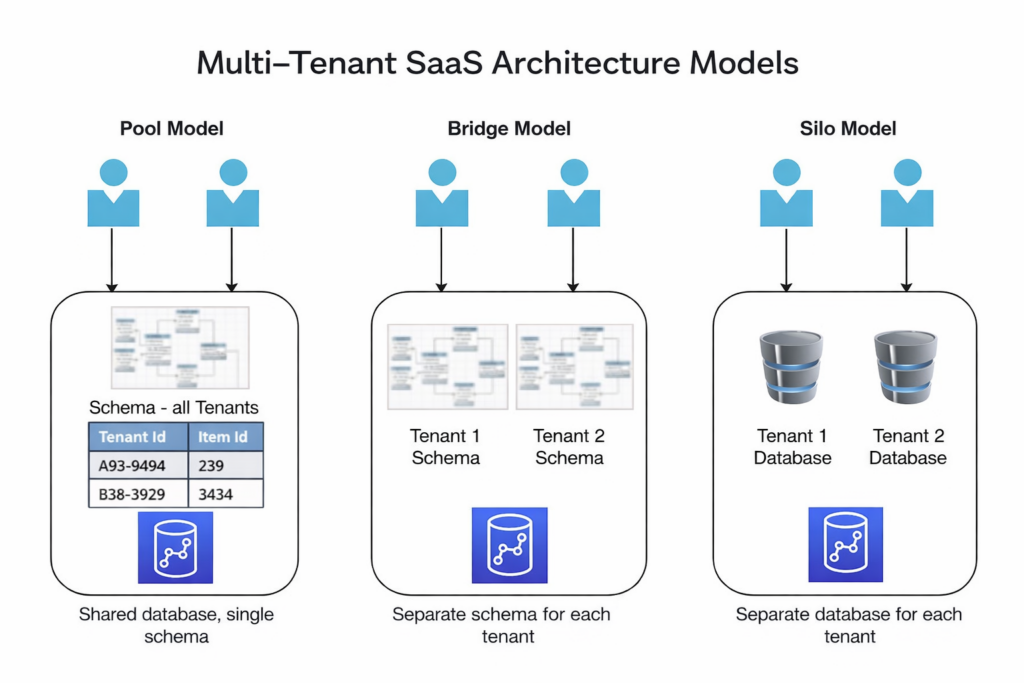
Model 1: Shared Database, Shared Schema
All tenants live in the same tables. Every row has a tenant_id column, and your application filters every query by that column, or you use Row-Level Security (RLS) in PostgreSQL to enforce it at the database level.
What’s compelling about it:
- Lowest infrastructure cost: one database to manage, back up, and monitor
- Easiest to scale horizontally: adding compute benefits to all tenants simultaneously
- Simplest schema migrations: one change, everyone updated
What will hurt you:
- A single missing WHERE tenant_id = ? clause is a data leak. A single missed tenant filter becomes a potential data exposure in shared schema models, and it requires strict enforcement of tenant-aware queries across every data access path.
- RLS policies must be tested continuously, not just at setup
- Subject to the worst noisy neighbor effects at the query level
Best for: High-volume B2C SaaS with thousands of tenants, uniform data models, and technically experienced teams comfortable with advanced PostgreSQL features.
Model 2: Shared Database, Separate Schemas
One database instance, but each tenant gets their own schema. tenant_123.users, tenant_456.users completely isolated table structures.
What’s compelling about it:
- Stronger isolation than shared schema: tenant data is physically separated at the schema level
- Per-tenant customization is more tractable
- Backup and restore per tenant is operationally cleaner
What will hurt you:
- Schema migrations become a coordination problem at scale. Applying a migration across 500 tenant schemas without downtime is a genuinely hard engineering problem
- You still share the underlying database instance, noisy neighbor effects persist at the compute and I/O level
- Operational complexity grows proportionally with tenant count
Best for: Mid-market SaaS with 100–500 tenants, where per-tenant customization is a real requirement, and teams have the operational maturity to manage migration complexity.
Model 3: Database Per Tenant (Silo Model)
Each saas tenant gets their own dedicated database instance. Maximum isolation with one tenant’s runaway query cannot affect another’s.
What’s compelling about it:
- Eliminates the noisy neighbor problem at the data tier entirely
- Non-negotiable for regulated industries: HIPAA, PCI-DSS, SOC 2 Type II environments where contractual data isolation is required
- Per-tenant performance tuning and independent scaling are possible
- Makes compliance audits significantly cleaner
What will hurt you:
- Infrastructure cost and operational complexity scale linearly with tenant count
- 500 tenants means 500 databases to monitor, patch, and back up
- Cross-tenant analytics and benchmarking require additional data aggregation layers
Best for: Enterprise SaaS with high-value customers, regulated industries, or any context where a customer requires contractual guarantees of data isolation.
|
Model |
Cost Efficiency |
Isolation Strength |
Migration Complexity |
Noisy Neighbor Risk |
|
Shared DB, Shared Schema |
⭐⭐⭐⭐⭐ |
⭐⭐ |
Low |
High |
|
Shared DB, Separate Schemas |
⭐⭐⭐⭐ |
⭐⭐⭐ |
Medium |
Medium |
|
Database Per Tenant |
⭐⭐ |
⭐⭐⭐⭐⭐ |
Low |
None |
|
Hybrid Model |
⭐⭐⭐⭐ |
⭐⭐⭐⭐ |
High |
Low |
📝Note: Most mature SaaS products we build end up at the hybrid model, standard-tier tenants in a shared pool, enterprise tenants in dedicated instances. It’s more complex to operate, but it lets you offer genuine isolation as a premium tier without rebuilding your entire architecture.
The Noisy Neighbor Problem: It Will Find You
If we had to name the single most underestimated challenge in saas multi tenant architecture, it’s the noisy neighbor problem. And it doesn’t announce itself during development; it shows up in production, usually at the worst possible moment.
The noisy neighbor problem occurs when one tenant’s activities overload shared resources, whether compute cycles, database capacity, network bandwidth, or message processing, degrading performance for all other tenants on the same infrastructure.
Here’s what it looks like: Tenant A is running a quarterly report that involves complex aggregations across three years of data. Their query saturates the database CPU. Basic lookups from Tenant B: a paying customer doing nothing unusual suddenly start timing out. They file a support ticket. Your SLA is broken. And you have no immediate fix because the problem is structural, not operational.
Related reading → Security Architecture for Healthcare Apps
We’ve seen this play out with a client whose shared PostgreSQL instance had an enterprise tenant importing millions of records during business hours. I/O bandwidth saturated. Transactional queries from smaller tenants began failing. The fix required emergency schema changes, read replica configuration, and a tense conversation with the enterprise customer about scheduling large imports off-peak.
How to mitigate it before it finds you:
- Per-tenant connection pooling: Use PgBouncer or a similar pooler with per-tenant pool limits. A poorly designed tenant client that opens a new connection per request can exhaust max_connections and lock everyone else out.
- Query timeout enforcement at the application layer: Set aggressive statement timeouts per tenant tier. A standard-plan tenant triggering a multi-second query should be killed, not allowed to saturate shared resources.
- Dedicated worker queues for premium tenants: Don’t let enterprise tenants and free-tier tenants share the same background job queue. Priority queuing with per-tier worker pools is essential.
- Rate limiting and quota enforcement: Every tenant should have documented resource limits: API calls per minute, database query budget per hour, and storage caps. Enforce them proactively, not reactively.
- Read replicas for analytics workloads: Route reporting and analytical queries to read replicas, keeping transactional query performance stable on the primary.
Tenancy Cloud Computing: What the Application Layer Must Get Right
Choosing the right database model is only half the architecture. Tenancy cloud computing requires the entire application layer to be tenant-aware, and this is where most bugs that cause cross-tenant data exposure actually live.
Tenant context propagation is the most critical discipline. Every request entering your system must establish tenant context immediately from the authentication layer, and that context must propagate through every service call, every database query, every background job, and every cache operation. A context that gets lost mid-stack is a data isolation failure waiting to happen.
How we handle this at Tech Exactly on cross platform mobile app development services builds with multi-tenant backends:
- Tenant ID is extracted from the JWT at the API gateway and attached to every downstream request header
- Every service receives tenant context explicitly, never inferred from other data
- Database queries are wrapped in tenant-scoped repository classes that automatically apply tenant filters. Individual developers never write raw queries without the abstraction layer enforcing isolation
- Background jobs carry tenant context in the job payload, not derived from environment or session
Feature flags and tenant configuration are the other areas where saas multi tenant products consistently under-invest. The impulse is to build a custom feature for one enterprise customer by branching the code.
✅Instead: build configuration over customization. Feature flags that enable or disable capabilities per tenant tier. Configurable business rules that live in tenant configuration records, not in conditional code. Branding and white-labeling through theme configurations, not separate deployments. This approach keeps your codebase unified while delivering the customization enterprise customers legitimately need.
Related reading → How to Build AI-Powered SaaS Applications
The Pitfalls That Will Cost You the Most
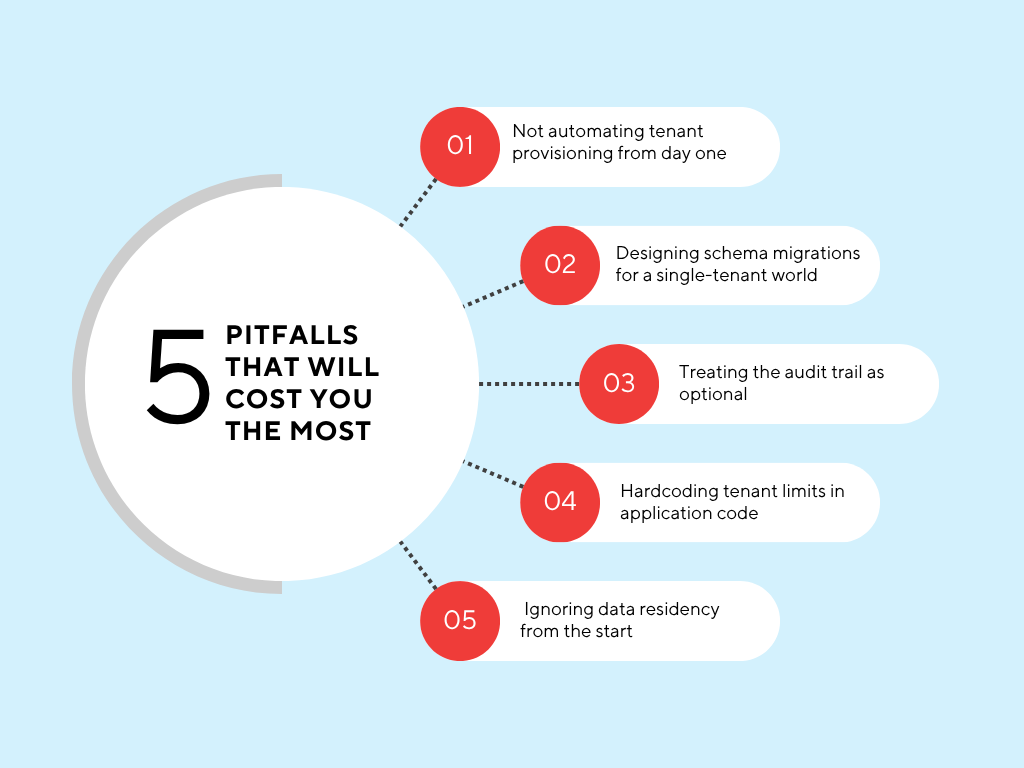
We’ve listed the architectural trade-offs. Now for the pitfalls, the decisions that look reasonable at the time and become expensive later.
Pitfall 1: Not automating tenant provisioning from day one
Manual tenant setup is fine for 10 customers. At 100, it’s a bottleneck. At 500, it’s a liability. When a sales deal closes on a Friday afternoon, your system should create the tenant record, set up the default configuration, provision any isolated resources, and send the welcome email without anyone touching a keyboard. Build the automation before you need it, not after you’ve promised a 24-hour onboarding SLA.
Pitfall 2: Designing schema migrations for a single-tenant world
In a single-tenant application, a database migration is a deployment step. In multi tenant systems with separate schemas or databases, a migration is a coordination problem. At 100 tenants, a sequential migration might take hours. You need migration tooling that runs migrations in parallel, handles failures gracefully, and maintains a migration state per tenant so partial runs can resume. Build this before you have the volume that makes it urgent.
Pitfall 3: Treating the audit trail as optional
Every action in a multi-tenant system needs to be attributable: which user, in which tenant, did what, at what time. This is the mechanism that lets you investigate when a customer says, “data X disappeared.” Without an audit trail, you’re guessing. IBM’s 2024 data breach report found that the average cost of a multi-tenancy-related breach reached $4.4 million.
Pitfall 4: Hardcoding tenant limits in application code
Rate limits, storage quotas, API call budgets these should live in tenant configuration records in the database, not in constants in your code. When you need to adjust a limit for a specific customer (and you will), doing it through a configuration change is a five-minute operation. Doing it through a code change, a PR review, and a deployment is a half-day exercise that creates risk.
Pitfall 5: Ignoring data residency from the start
EU GDPR, HIPAA, and regional data-residency laws increasingly require that patient or customer data be stored within specific geographic boundaries. Retrofitting data residency into a cloud multi tenancy architecture that wasn’t designed for it is expensive and disruptive. If you have any reasonable expectation of serving EU customers or enterprise customers with data residency requirements, design your tenant routing to support regional deployments from the start.
Best Practices We Apply on Every Multi-Tenant Build
Whether we’re delivering Custom Mobile App Development Services in USA with a multi-tenant backend, building enterprise SaaS for Custom Mobile App Development Services in UK clients, or architecting cross platform mobile app development services on shared infrastructure, these are the practices we apply consistently.
- Start with the tenant context in the authentication layer, not the application layer. By the time a request reaches your business logic, the tenant context should already be validated and immutable. Never trust the tenant context provided by user input.
- Use Row-Level Security in PostgreSQL for shared schema models, but test it continuously. RLS is powerful, but it’s also easy to misconfigure. Include RLS policy tests in your CI pipeline. A policy regression should fail the build, not reach production.
- Assign per-tenant encryption keys via a KMS. Per-tenant encryption keys mean a compromised key affects exactly one tenant’s data, not everyone’s. Key rotation per tenant is also operationally clean. This is table stakes for any SaaS product targeting regulated industries.
- Build a tenant health dashboard before you build tenant-facing features. You need visibility into per-tenant resource consumption, query latency, API usage, and error rates before problems surface in customer support tickets. Instrument from day one.
- Design for offboarding, not just onboarding. When a customer cancels, can you export their data cleanly, delete it completely, and confirm deletion with an audit record? GDPR requires this. Enterprise customers will ask for it. Build the offboarding flow before a customer demands it.
- Treat schema migrations as a first-class engineering discipline. Document your migration strategy, build migration tooling that handles parallel execution and resumable failures, and test migrations against a representative tenant dataset before running them in production.
Related reading → How SMBs Can Integrate AI into Existing Software Systems
When to Start with Single-Tenant and Move to Multi-Tenant Later
This is a question we get asked regularly, and the honest answer is: starting single-tenant and migrating to multi-tenant is significantly harder than building multi-tenant from the start. The data model changes, the application logic changes, and the infrastructure model changes. We’ve done it for clients who outgrew their original architecture, and it’s always a multi-month project.
The cases where starting single-tenant makes sense:
- You have two or three enterprise customers with highly customized requirements and no immediate plans to scale to dozens more
- You’re in a regulated industry where the compliance requirements for multi-tenancy are too complex for your current team capacity
- Your customers are paying prices that absorb the higher operational cost of dedicated instances
What we at Tech Exactly prefer doing, in most other cases, particularly for teams building scalable B2B SaaS with a broad customer base, is design for saas multi tenant architecture from the start, even if you only have a handful of tenants initially. The patterns aren’t significantly harder to implement on a small scale, and the cost of retrofitting grows exponentially as your product matures. If you are looking for custom Mobile App Development Services in UK and have a question around this, feel free to write to us at info@techexactly.com
Let's Start Your Project Today
Ready to build your App with us? Reach out now – our experts are just one click away.
Frequently Asked Questions
Multi tenant meaning in SaaS is a design pattern where a single running application instance serves multiple customers simultaneously, with their data and configurations logically isolated. Each customer, a saas tenant, operates as though they have a private dedicated environment, even though they share the underlying infrastructure, codebase, and in many models, the same database instance.
Cross-tenant data exposure through missing or misconfigured tenant context. In shared schema models, a single missing tenant filter in a database query can expose one tenant's data to another. In any model, insufficient tenant context propagation through the application stack, where tenant identity gets lost between service calls or background jobs, creates the same risk. Combine this with inadequate audit logging, and you have a breach that's both likely and difficult to detect.
Through a combination of per-tenant connection pooling, query timeout enforcement by tier, dedicated worker queues for premium tenants, rate limiting, and storage quotas enforced at the application layer, and routing analytical workloads to read replicas. For enterprise tenants with contractual performance SLAs, the only complete solution is database-per-tenant isolation; shared infrastructure, by definition, cannot provide guaranteed resource availability.
When your customer base spans multiple segments with genuinely different requirements: SMB tenants who benefit from cost-efficient shared infrastructure, and enterprise tenants who require contractual data isolation, custom compliance postures, or guaranteed performance. A hybrid model serves standard-tier tenants from a shared pool while offering database-per-tenant deployment as a premium tier. It's architecturally more complex to operate, but it's the model that lets you grow upmarket without rebuilding your infrastructure.
Pallabi Mahanta, Senior Content Writer at Tech Exactly, has over 5 years of experience in crafting marketing content strategies across FinTech, MedTech, and emerging technologies. She bridges complex ideas with clear, impactful storytelling.

