Tech Exactly's App Turnaround Expertise
Say goodbye to cost overruns, revenue loss, and stagnant user growth. We specialize in turning around app-based companies, providing a seamless development experience for exponential growth

Web Application Testing & QA Services
Functional, performance, security, and penetration testing for web and mobile applications. We test across browsers, devices, and compliance standards, so your app ships without surprises.
Top Rated
Clients
Ask AI to summarize this page
Save time with an instant, easy-to-read summary.
Transforming Businesses with Proven Results
Faster development, greater efficiency, trusted globally, and driven by referrals.
savings with AI-powered Engineering
users trust our products
efficiency boost for businesses
of new clients come from referral
Our Web Application Testing Services
End-to-end QA and web app testing services — covering every layer of your web application before it reaches users.
Functional Testing
We validate every feature against requirements: user flows, form submissions, data processing, business logic, and edge cases. Nothing ships without working as intended.
Performance & Load Testing
Simulate real user traffic with k6 and JMeter. We identify bottlenecks before they hit production — API response times, database query latency, and infrastructure limits under concurrent load.
Security & Penetration Testing
OWASP Top 10 assessment, vulnerability scanning, authentication testing, and manual pen testing. We find the attack vectors before bad actors do, like SQL injection, XSS, CSRF, broken access control.
Usability Testing
Real-user testing across your core flows, including onboarding, key features, checkout, and error states. We surface friction points that analytics can't capture and prioritize fixes by impact.
Compatibility & Cross-Browser Testing
Testing across Chrome, Firefox, Safari, Edge, and mobile browsers. We cover major OS combinations and screen sizes, so your app behaves consistently for every user.
Accessibility Testing
WCAG 2.1 and ADA compliance testing, with screen reader compatibility, keyboard navigation, color contrast, and focus management. This helps meet legal requirements and serve users with disabilities.
Test Automation
Automated test suites with Cypress, Playwright, and Selenium. Integrated into your CI/CD pipeline so every commit triggers a full regression run — faster feedback, fewer manual test cycles.
Compliance Testing
HIPAA, PCI-DSS, GDPR, and SOC 2 compliance verification. We check audit logging, data encryption, access controls, and consent management against the specific standards your app must meet.
API Testing
Contract testing, integration testing, and security testing for REST and GraphQL APIs. We validate response schemas, error handling, rate limiting, authentication, and data integrity.
Mobile App Testing & Security
iOS, Android, and cross-platform testing, including including security and penetration testing for mobile applications.
Mobile App Functional Testing
End-to-end functional testing on real iOS and Android devices — user flows, push notifications, offline behavior, deep links, and platform-specific features.
Mobile App Security Testing
OWASP Mobile Top 10 assessment — insecure data storage, improper authentication, sensitive data exposure, and client-side injection on both iOS and Android.
Mobile App Performance Testing
Battery consumption, memory usage, app launch time, and network performance on low-end devices and throttled networks — where most real users actually are.
Mobile App Penetration Testing
Manual and automated pen testing for iOS and Android — runtime analysis, API security, certificate pinning, and privilege escalation. Includes a findings report with remediation guidance.
Testing Tools & Tech Stack
Industry-standard tools across functional, performance, security, and automation testing.
Why Choose Tech Exactly for Testing & QA
As a trusted web application testing company, we have a testing-first mindset — built into development, not bolted on at the end.
Real Devices, Not Just Emulators
Our web application testing services include testing on actual iOS and Android devices across major manufacturers — Samsung, Google Pixel, OnePlus, iPhone. Browser testing covers Chrome, Firefox, Safari, and Edge at real screen sizes.
Security Testing With Every Engagement
Every web application testing service engagement includes OWASP Top 10 coverage for both web and mobile applications. We do not treat security as a separate add-on.
Compliance-Aware Testing
We've tested HIPAA-compliant healthcare apps, PCI-DSS fintech platforms, and GDPR-regulated SaaS products. Our expertise makes us a trusted choice for businesses looking for professional test my app and website services.
CI/CD Integration
Automated test suites integrated directly into your pipeline. Every pull request triggers a regression run. Broken builds are caught before they reach staging — not after.
Detailed Pen Test Reports
Security and penetration testing reports include CVSS severity scores, reproduction steps, affected endpoints, and prioritized remediation guidance — not just a list of vulnerabilities.
Embedded or Standalone Engagements
Work with us as an embedded QA team during development, or bring us in for a standalone audit before a major release. We adapt to your workflow.
Take a look at our Case Studies
We are proud of what we have built. Let us walk you through our projects.
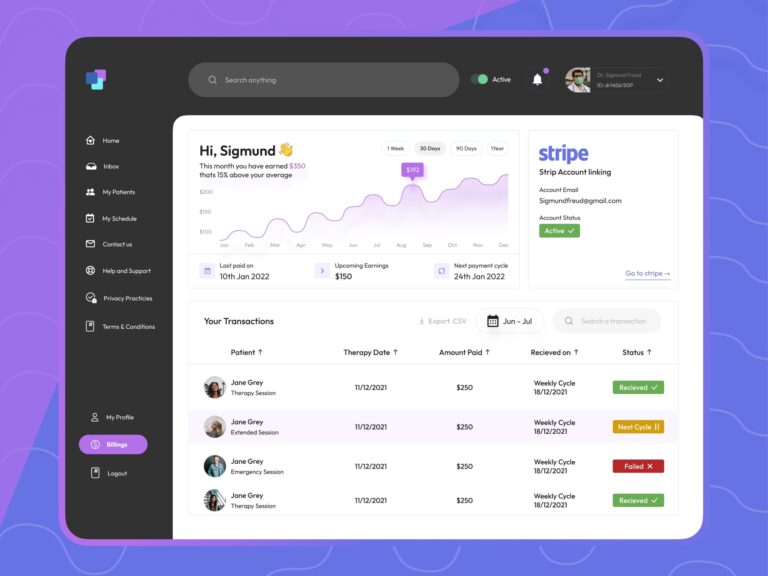
Learn about how we delivered a HIPAA-compliant website that offers online therapy sessions in NYC
Making mental healthcare ready, available, and cheap for everyone by delivering a comprehensive web application in accordance with HIPAA requirements
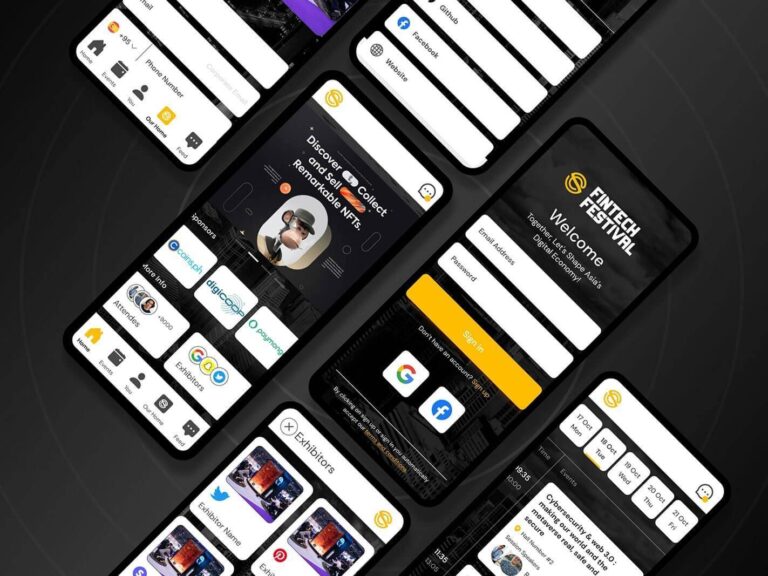
Developing a World-Class Mobile App for the World Fintech Festival Philippines
An intuitive, feature-rich app mobile app for seamless event access and engagement
Optimal user experience
Easy booking of tickets
Quick access to all event information

IEC 62304-Compliant Mobile App for Accurate Test Interpretation
A medical-grade mobile app to deliver ~ 70% precise interpretation of home diagnostic tests
Built under IEC 62304 for full compliance
Instant, accurate image analysis
Full traceability and validation
Our Testing Process
A structured QA process — from requirements analysis to sign-off.
Step 1 — Requirements Analysis & Test Planning
We review your requirements, user stories, and acceptance criteria. We define the test scope, coverage strategy, risk areas, and test environments — before writing a single test case.
Step 2 — Test Design & Environment Setup
Test cases written for functional, performance, security, and compatibility scenarios. CI/CD integration configured so automated tests run on every commit. Staging environment parity with production verified.
Step 3 — Test Execution & Defect Reporting
Manual and automated test execution across all defined scenarios. Defects logged with severity, reproduction steps, and evidence. Daily status updates and a live defect dashboard throughout.
Step 4 — Sign-Off & Regression
Final regression run before release. Go/no-go decision based on exit criteria agreed at the start. Full test report with coverage metrics, defect summary, and outstanding risk items delivered.
Hear From Our Clients
Read and learn why you should choose our web app testing service
"I’m most impressed with Tech Exactly’s ability to understand our challenges and come up with options to resolve them."
With other vendors I’ve worked with, I have to spend a lot of time explaining the challenge to them, and sometimes, they still don’t understand it. Tech Exactly takes the time to listen to us and offers us 3 – 5 different options to achieve the expected results.
Eric Shepherd
Foundation for Talent Transformation
“They are forthcoming, prompt, meticulous, sincere, punctual, and very professional. It's a joy to work with them!“

Akhil Chandra
Founder & Partner, Epiphany Labs

+ 0 %
Increase in free to paid subscriptions
“They’ve done a great job of meeting goals and deadlines as well as producing what was described in the scope of work.“

Kevin Eldredge
CAO, SSA Group

+ 0 %
Improvement in sales reconciliations timeline.
“They are so humble that even when the project is done, they always answer what we ask.“

Junie De Castro
World Fintech Festival Philippines
+ 0 %
Increase in user registrations and engagement
You will be in Good Care
We have worked with startups to multinational companies & we are well-versed in the challenges so relax
Frequently Asked Questions
As a full-service web application testing company, we offer functional testing, performance and load testing, security and penetration testing, usability testing, compatibility and cross-browser testing, accessibility testing (WCAG 2.1/ADA), test automation, API testing, and compliance testing (HIPAA, PCI-DSS, GDPR). We handle web and mobile — iOS, Android, and cross-platform apps.
Yes. We provide manual and automated penetration testing for iOS and Android apps — covering OWASP Mobile Top 10, API security, insecure data storage, authentication weaknesses, and runtime analysis. Every engagement includes a detailed findings report with CVSS severity scores and remediation guidance.
A standard OWASP Top 10 security assessment for a web application takes 3–7 business days, depending on the size and complexity of the application. A full penetration test with manual exploitation and detailed reporting typically takes 1–3 weeks. As part of our web app testing services, we can scope the engagement precisely after a brief technical review.
Yes. We set up automated test suites using Cypress, Playwright, or Selenium and integrate them with GitHub Actions, GitLab CI, Jenkins, or CircleCI. Every commit triggers a regression run, and results are reported directly in your pull request workflow.
Yes. We've tested healthcare applications for HIPAA compliance — encrypted data handling, audit logging, access controls, and BAA-covered infrastructure. For fintech applications, we verify PCI-DSS controls — tokenized payment handling, cardholder data protection, and network security requirements.
Businesses looking for reliable test my app and website services often need both QA testing and penetration testing. QA testing validates that your application works correctly — functional, performance, usability, and compatibility. Penetration testing is a security-specific exercise where our team actively attempts to exploit vulnerabilities, just like a real attacker would. Both are important — QA ensures the app works; pen testing ensures it's secure.
Yes. We test React Native and Flutter apps across iOS and Android — functional testing, platform-specific behavior validation, performance testing on real devices, and security testing for the native bridge and API layer.
Both. We work as an embedded QA team during active development sprints, or we come in for a standalone testing engagement before a major release. We also offer ongoing security monitoring and regression testing retainers for production applications.
Comprehensive web application testing services help detect functional issues, security gaps, performance bottlenecks, and compatibility problems before users experience them. Working with an experienced web application testing company reduces production risks and improves overall application reliability.
Businesses launching new digital products, scaling existing platforms, or preparing for compliance audits often use test my app and website services to validate quality, security, and performance. A professional web application testing service helps ensure your app delivers a stable and consistent user experience across devices and browsers.
Ready to Get Started?
Get a free quote and see what we can do for you.
